
One of the core functions of our business is the processing of data, which means data privacy and information security are two of our highest priorities. We recently had an internal workshop with our global security manager about the idea of a ‘security culture’ – taking information security beyond training and assessments, and into the realm of the ‘group subconscious’.
Most organizations create awareness of data protection and security through training and providing documents, policies and procedures to their staff. But awareness doesn’t necessarily change behavior, and although holding regular training sessions will tick an audit box, this may not be enough to actually prevent an incident.
The truth is . . . no matter how well documented your procedures or how clear your security policies, if you have a weak security culture, your organisation is vulnerable.
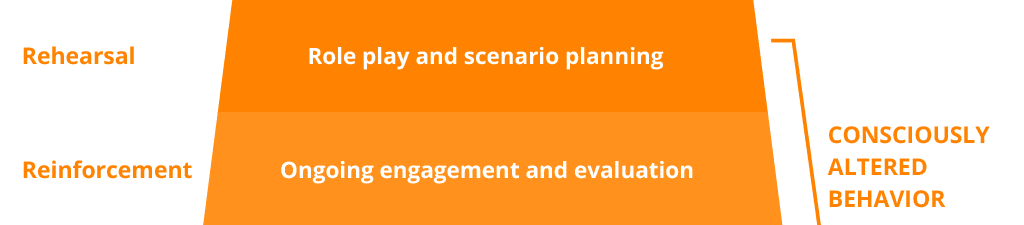
To create a culture of security, you need to move beyond awareness by creating a program that will teach staff how to recognize and avoid risky behavior and what to do if there is an attempt to breach your security. Once the group is conscious of the right response to security, ongoing engagement and evaluation will reinforce this behavior until it becomes the group norm. At that stage, the group becomes self-governing and the right behavior is embedded, culturally.

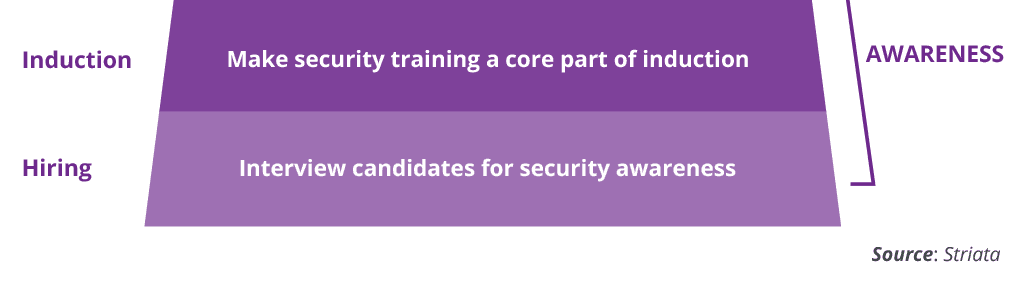
Awareness – hiring, induction and evaluation
If you have already created awareness amongst existing staff, bringing new people on-board shouldn’t add to your security agenda. Make interviewing for ‘security smarts’ part of your hiring process, so that you select individuals who already have the right attitude and approach to information security.
Make security training a core component in your induction program and include existing staff that may need a refresher. Make everyone complete assessments that test their understanding of the importance of information security, the potential risks and the required response.
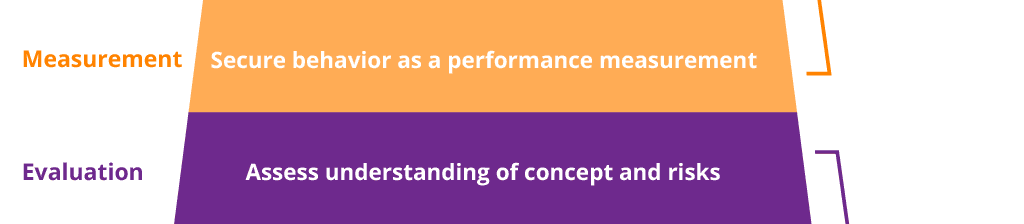
Consciously altered behavior – measurement, reinforcement and rehearsal
To really change behavior, you have to align how people are measured to your desired outcome. If information security is not part of an individual’s key performance criteria, it will not be top of mind.
Use your performance management program to regularly bring information security into the spotlight. Sharing knowledge and doing assessments are key, but reading an instruction and actually executing it correctly under pressure are different. Don’t leave the right behavior to chance – include role playing and scenario plotting in your security training.
Instinctive behavior – cohesion to culture
Once the right behavior is embedded into the culture of your organization, the group will start to police itself. Employees will be empowered to call someone out if they leave confidential documents on a desk or their workstation unlocked. Behavior that puts the organization at risk – either physically or digitally – will become extremely uncomfortable. Clicking on a random attachment or sharing passwords or key cards will simply be unacceptable to the group.
Building a security culture means embedding risk averse behavior so deeply into the foundation of an organization that doing the right thing becomes instinctive and effortless.















